Do you know who has access …
- … to your Digital ID?
- … to your Digital Health?
- … to your Digital Shopping?
- … to your Travel Restrictions?
- … to your Central Bank Digital Currency?
Chances are, the answer is
‘Don’t know!’
But there is something that can be done to secure your online privacy in our digital age.
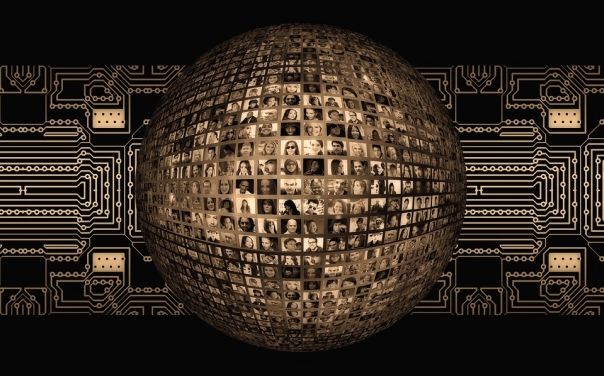
In our increasingly connected digital world, protecting personal information has become a matter of utmost importance. Neglecting online privacy can have severe consequences, including identity theft, financial fraud, and cybercrime. In a world where technology and the internet play a central role in our daily lives, it is imperative that we take steps to secure our digital footprint and protect our personal information from exploitation by governments, corporations, and cybercriminals.
The collection and use of personal information by governments and corporations is a significant threat to online privacy. Governments can gather data through various sources, such as databases, surveillance programs, and data retention laws. This information can range from basic personal details to online behavior, purchasing habits, social media contributions, and even health records. The use of this information for national security or to monitor citizens’ activities often happens without their consent or knowledge.
Corporations collect personal information through tracking technologies, such as cookies and browser fingerprinting, and data-sharing agreements. This information is used for marketing and advertising purposes, such as targeted advertisements and personalization, without individuals’ consent or knowledge, leaving them vulnerable to exploitation and privacy violations.
The collection and use of personal information can compromise an individual’s online and physical security. As former NSA and CIA Director Michael Hayden famously said:
“We kill people based on metadata.” *
* What is metadata?
Metadata describes other data, often secret data, for instance, telephone numbers, to whom you spoke, how long you spoke, which country you called …
This highlights the importance of understanding the dangers of metadata and the need to protect our personal information.
We all experienced this nightmare since years, but more so from 2020 until today, and it still continues in certain countries! We just opened the Pandora box!
Open-source software is a type of software that can be freely accessed and modified by anyone. This makes it more secure and transparent compared to proprietary software. In the context of online privacy, open-source software can offer secure and anonymous ways to access the internet by encrypting the user’s data and hiding their IP address (a unique numerical label assigned to every device connected to the internet, used to identify and communicate with it). This helps to protect the user’s online privacy and personal information from being collected and used by governments and corporations. These last two identities use this type of software to protect themselves.
In addition to the use of secure e-mail providers and encrypted browsers, there are several other steps that individuals can take to protect their online privacy:
- Use strong and unique passwords: Strong passwords are essential for protecting your online accounts from cyberattacks. Use a combination of letters, numbers, and symbols, and make sure that each password is unique to each of your accounts.

- Enable two-factor authentication: Two-factor authentication is a security measure that requires a second factor, typically a code sent to / given by your phone, in addition to a password to access an online account, providing an extra layer of protection against unauthorized access.
- Be cautious with personal information: Be careful about the personal information that you share online and documents that you throw away in the garbage or dust bin. Think twice before posting sensitive information, such as your home address or financial information, on social media.
- Use a virtual private network (VPN): A VPN encrypts your internet traffic and protects your online activities from prying eyes. A local VPN can save you a lot of money too.
- Keep software and systems up-to-date: Software updates often contain security patches that protect against new threats, so make sure that your software and systems are always up-to-date (Windows, Linux, MacOS, Android, iOS, …).
- Be aware of phishing scams: Phishing scams are a common way for cyber-criminals to steal personal information. Be cautious of e-mails, SMS or messages that ask for sensitive information, such as passwords or credit card numbers, and always verify the source before providing any information. Even in the dating world (see my previous article).
- Review privacy settings: Regularly review the privacy settings of your social media accounts and other online services to ensure that you are comfortable with the information that is being shared – they changed these settings often without telling anything.
In conclusion, protecting our online privacy has become increasingly important in our digital age, more so after 2020. The collection and use of personal information by governments and corporations, as well as the rise of cyberthreats, have made it imperative for individuals to take steps to protect their personal information and online security. From using strong passwords and two-factor authentication to utilizing privacy-focused software and VPNs, there are several measures we can take to safeguard our online privacy. It’s important to note that the risks to our personal information and security are real and ongoing, and that we must remain vigilant in our efforts to protect it. By being mindful of the threats and taking proactive steps to secure our online presence, we can ensure that our personal information remains protected and our privacy remains intact.
Are you looking for ways to ensure the privacy and security of yourself, your family, and your business?
Our training courses may be just what you need. Do not wait until it is too late. Our courses adopt a hands-on approach, prioritizing practical application over theory.
Get in touch with us at info [at] digitaltran.eu
After considering your application, we will share a link with you where we can in all security do our training. Groups remain small so that everybody can follow.
Here are just some examples where governments want to control everything with the help of social media (corporations):
“Justin Trudeau Hijacks Canada’s Healthcare ...”
(link to the ‘Gateway Pundit’ with officials’ videos)
Here is a video about the internet censorship – is it coming?

